
News
发布日期:2023-10-27 浏览次数:3587 来源:WOLFLAB杨广成
EI CCNP培训企业基础架构课程-EIGRP拓扑变更时查询机制详解

WOLF-LAB网络技术实验室思科认证CCNP企业基础架构培训课程考试、学习咨询了解联系网站客服!
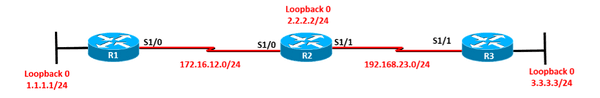
实验拓扑如上图所示,配置接口ip地址,R1 R2 R3上运行EIGRP 90:
R1: interface Loopback0 ip address 1.1.1.1 255.255.255.0 interface Serial1/0 no shutdown ip address 172.16.12.1 255.255.255.0
router eigrp 90 network 1.1.1.1 0.0.0.0 network 172.16.12.1 0.0.0.0 no auto-summary | R2: interface Loopback0 ip address 2.2.2.2 255.255.255.0 interface Serial1/0 no shutdown ip address 172.16.12.2 255.255.255.0 interface Serial1/1 no shutdown ip address 192.168.23.2 255.255.255.0 router eigrp 90 network 2.2.2.2 0.0.0.0 network 172.16.12.2 0.0.0.0 network 192.168.23.2 0.0.0.0 no auto-summary |
R3: interface Loopback0 ip address 3.3.3.3 255.255.255.0 interface Serial1/1 no shutdown ip address 192.168.23.3 255.255.255.0 router eigrp 90 network 3.3.3.3 0.0.0.0 network 192.168.23.3 0.0.0.0 no auto-summary | |
1、在R1 R2 R3上开启debug eigrp packets query reply ack。将R1的loopback接口shutdown,观察各路由器的query、reply包的传递情况,理解EIGRP DUAL扩散查询的方式。
R1、R2、R3: debug eigrp packets query reply ack |
R1: interface Loopback0 shutdown |
R1: *Oct 1 18:24:27.391: EIGRP: Enqueueing QUERY on Serial1/0 nbr 172.16.12.2 iidbQ un/rely 0/0 peerQ un/rely 0/0 serno 91-91 *Oct 1 18:24:27.395: EIGRP: Sending QUERY on Serial1/0 nbr 172.16.12.2 //向R2发出Query --- 1 *Oct 1 18:24:27.395: AS 90, Flags 0x0, Seq 94/90 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 serno 91-91 *Oct 1 18:24:27.455: EIGRP: Received ACK on Serial1/0 nbr 172.16.12.2 //收到R2回复的Ack --- 4 *Oct 1 18:24:27.459: AS 90, Flags 0x0, Seq 0/94 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 *Oct 1 18:28:11.467: AS 90, Flags 0x0, Seq 0/101 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 *Oct 1 18:28:11.483: EIGRP: Received REPLY on Serial1/0 nbr 172.16.12.2 //收到R2回复的Reply --- 14 *Oct 1 18:28:11.487: AS 90, Flags 0x0, Seq 105/101 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0 *Oct 1 18:28:11.491: EIGRP: Sending ACK on Serial1/0 nbr 172.16.12.2 //向R2回复Ack --- 15 *Oct 1 18:28:11.491: AS 90, Flags 0x0, Seq 0/105 idbQ 0/0 |
R2: *Oct 1 18:28:11.355: EIGRP: Received QUERY on Serial1/0 nbr 172.16.12.1 //收到R1的Query --- 2 *Oct 1 18:28:11.359: AS 90, Flags 0x0, Seq 100/100 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0 *Oct 1 18:28:11.359: EIGRP: Enqueueing ACK on Serial1/0 nbr 172.16.12.1 *Oct 1 18:28:11.367: EIGRP: Sending ACK on Serial1/0 nbr 172.16.12.1 //向R1回复Ack --- 3 *Oct 1 18:28:11.367: AS 90, Flags 0x0, Seq 0/100 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 1/0 *Oct 1 18:28:11.391: EIGRP: Sending QUERY on Serial1/1 nbr 192.168.23.3 //向R3发出Query --- 5 *Oct 1 18:28:11.395: AS 90, Flags 0x0, Seq 103/99 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 serno 131-131 *Oct 1 18:28:11.427: EIGRP: Received ACK on Serial1/1 nbr 192.168.23.3 //收到R3回复的Ack --- 8 *Oct 1 18:28:11.427: AS 90, Flags 0x0, Seq 0/103 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 *Oct 1 18:28:11.435: EIGRP: Received REPLY on Serial1/1 nbr 192.168.23.3 //收到R3回复的Reply --- 10 *Oct 1 18:28:11.439: AS 90, Flags 0x0, Seq 100/103 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0 *Oct 1 18:28:11.447: EIGRP: Sending ACK on Serial1/1 nbr 192.168.23.3 //向R3发出Ack --- 11 *Oct 1 18:28:11.447: AS 90, Flags 0x0, Seq 0/100 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 1/0 *Oct 1 18:28:11.467: EIGRP: Enqueueing REPLY on Serial1/0 nbr 172.16.12.1 iidbQ un/rely 0/1 peerQ un/rely 0/0 serno 132-132 *Oct 1 18:28:11.475: EIGRP: Sending REPLY on Serial1/0 nbr 172.16.12.1 //向R1回复Reply --- 13 *Oct 1 18:28:11.475: AS 90, Flags 0x0, Seq 105/101 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 serno 132-132 *Oct 1 18:28:11.491: EIGRP: Received ACK on Serial1/0 nbr 172.16.12.1 /收到R1回复的Ack --- 16 *Oct 1 18:28:11.491: AS 90, Flags 0x0, Seq 0/105 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 |
R3: *Oct 1 18:28:11.407: EIGRP: Received QUERY on Serial1/1 nbr 192.168.23.2 //收到R2的Query --- 6 *Oct 1 18:28:11.411: AS 90, Flags 0x0, Seq 103/99 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0 *Oct 1 18:28:11.423: EIGRP: Sending ACK on Serial1/1 nbr 192.168.23.2 //向R2回复Ack --- 7 *Oct 1 18:28:11.423: AS 90, Flags 0x0, Seq 0/103 idbQ 1/0 iidbQ un/rely 0/0 peerQ un/rely 1/0 *Oct 1 18:28:11.443: EIGRP: Enqueueing REPLY on Serial1/1 nbr 192.168.23.2 iidbQ un/rely 0/1 peerQ un/rely 0/0 serno 151-151 *Oct 1 18:28:11.451: EIGRP: Sending REPLY on Serial1/1 nbr 192.168.23.2 //向R2回复Reply --- 9 *Oct 1 18:28:11.455: AS 90, Flags 0x0, Seq 100/103 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 serno 151-151 *Oct 1 18:28:11.475: EIGRP: Received ACK on Serial1/1 nbr 192.168.23.2 //收到R2的Ack --- 12 *Oct 1 18:28:11.475: AS 90, Flags 0x0, Seq 0/100 idbQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/1 |
2、通过在R2上S1/1口设置ACL,阻止R3发送过来的所有EIGRP包,通过设置holddown time到最长,使R2-R3之间EIGRP邻居关系不会DOWN,然后shut down R1的loopback口,观察EIGRP的拓扑表,学习EIGRP的SIA状态, 以及cisco设计SIA-Query/SIA-Reply两种报文的意义。
R3: interface Serial1/1 ip hold-time eigrp 90 65535 //先将R3的holddown timer设置为最大 | |
R2: access-list 100 deny eigrp 192.168.23.3 0.0.0.0 any access-list 100 permit ip any any interface Serial1/1 ip access-group 100 in
R2#show ip eigrp neighbors IP-EIGRP neighbors for process 90 H Address Interface Hold Uptime SRTT RTO Q Seq (sec) (ms) Cnt Num 0 192.168.23.3 Se1/1 65530 02:08:06 387 2322 0 101 1 172.16.12.1 Se1/0 13 02:42:21 40 240 0 102
解析:即使R2的S1/1接口调用了ACL,过滤R3发出的EIGRP的包,也包括Hello包,此时R2-R3之间的邻居关系暂时也不会down。Hold时间从65535秒开始倒计时。
| |
R1: interface Loopback0 shutdown | |
R1: R1#show ip eigrp topology IP-EIGRP Topology Table for AS(90)/ID(1.1.1.1) A 1.1.1.0/24, 1 successors, FD is Inaccessible 1 replies, active 00:01:28, query-origin: Local origin Remaining replies: via 172.16.12.2, r, Serial1/0
R1#show ip eigrp topology IP-EIGRP Topology Table for AS(90)/ID(1.1.1.1) A 1.1.1.0/24, 1 successors, FD is Inaccessible 1 replies, active 00:01:34, query-origin: Local origin, retries(1) Remaining replies: via 172.16.12.2, r, Serial1/0
| R2: R2#show ip eigrp topology IP-EIGRP Topology Table for AS(90)/ID(2.2.2.2) A 1.1.1.0/24, 1 successors, FD is Inaccessible, Q 1 replies, active 00:01:24, query-origin: Successor Origin Remaining replies: via 192.168.23.3, r, Serial1/1
R2#show ip eigrp topology IP-EIGRP Topology Table for AS(90)/ID(2.2.2.2) A 1.1.1.0/24, 1 successors, FD is Inaccessible, Qqr 1 replies, active 00:01:36, query-origin: Successor Origin Remaining replies: via 192.168.23.3, r, Serial1/1 SIA-Stuck: 1 peers Peers: via 192.168.23.3, s, Serial1/1 |
解析: ① 由于R3回复的Ack与Reply没有到R2上,R2就不会向R1回复Reply,所以此时在R1和R2上的EIGRP拓扑表中看到1.1.1.0/24这条路由为Active状态; ② R1迟迟收不到R2回复的Reply,R1会在active状态90s的时候向R2发送SIA-Query,R2收到以后会向R1回复SIA-Reply,此时R1即可确认R1-R2之间的状态是正常的。即使到了active状态3分钟,R1-R2之间的邻居也不会down。 ③ 由于R3回复的Ack与Reply没有到R2上,R2到了active状态3分钟的时候,清除与R3的EIGRP邻居,此时R2相当于边界路由器了,向R1回复Reply。 | |
3、在R1 R2 R3上修改Active Time为1分钟。并在R1-R2之间开启EIGRP的认证,密码为cisco。
R1、R2、R3: router eigrp 90 timers active-time 1 //默认是3分钟 |
R1、R2: key chain A key 1 key-string cisco
interface Serial1/0 ip authentication mode eigrp 90 md5 ip authentication key-chain eigrp 90 A |
4、把R3配置成为EIGRP Stub路由器,设置为Stub receive-only, R1上能否看到R3的loopback路由。
R3: router eigrp 90 eigrp stub receive-only //此时R1上看不到3.3.3.0/24路由。R3不会向邻居通告任何路由。 |
5、在R3上增加一条静态路由 33.3.3.0/24 指向null0, 重分布该静态路由进EIGRP,通过配置stub redistributed /static,在R1上可以看到33.3.3.0/24路由。
R3: ip route 33.3.3.0 255.255.255.0 null 0
router eigrp 90 redistribute static eigrp stub redistributed static
解析:stub后面配置redistributed参数可以将所有重分布的路由通告给邻居;而stub后面配置static参数只会将重分布静态的路由通告给邻居。 |
6、删除第5题的配置。将R2设置为stub路由器,通过配置leak-map,要求在R1上可以看到3.3.3.0/24路由。
R3: router eigrp 90 no eigrp stub |
R2: access-list 1 permit 3.3.3.0 route-map LEAK permit 10 match ip address 1
router eigrp 90 eigrp stub leak-map LEAK
解析:通告leak-map做路由泄露,只能针对动态学到的路由才有效。对于自己始发的路由,无效。 |
7、在R1上使用distance 255的方法过滤33.3.3.0/24,观察实验现象,是否生效。
R1: access-list 1 permit 33.3.3.0 router eigrp 90 distance 255 172.16.12.2 0.0.0.0 1 //没有生效,R1的路由表中可以看到33.3.3.0/24。
解析:distance xx此方法只能修改EIGRP内部路由的管理距离,对于DEX路由是无效的。 可以通过distance eigrp xx yy来修改EIGRP管理距离,xx为内部路由管理距离,yy为外部路由管理距离。 |
8、在R3上使用distribute-list过滤这条33.3.3.0/24,在R1 R2上看不到此路由,不能使用基于接口的过滤。
R3: access-list 1 deny 33.3.3.0 0.0.0.0 access-list 1 permit any
router eigrp 90 distribute-list 1 out static //基于协议的过滤,只能用于出向。针对重分布静态的路由,发出时做过滤。 |
WOLFLAB官方微信:17316362402
WOLFLAB官方QQ:2569790740
思科认证CCNP培训课程考试、学习咨询联系WOLF-LAB网络技术实验室